Johann's Research
I'm not sure if my stuff is really research, but this is some of the stuff that I'm busy with:
High Performance Node - WEP/WPA
One of the requirements of the High Performance Node is to have WEP or WPA enabled between the wireless links of the mesh nodes. This is one of the functionalities that we would like to sort out before we install any of the nodes in the field. It's very difficult to change the encryption mode after an installation because the mesh nodes will lose connectivity if one node is upgraded to use WEP, while another is still using older software without WEP.
WEP and WPA are both methods to enable the encryption of data that it is send over the air. WEP (Wired equivalence privacy) is an older standard and it makes use of a WEP encryption engine while the newer WPA standard added the use of an AES encryption engine. WEP encryption has some security flaws embedded into the protocol and there are several tools available on the Internet that can crack WEP keys. These tools are more effective with the cracking of 64bit WEP keys than with 128bit keys and they require a large amount of captured data and processing power to crack a key. Note that not all WEP keys can be cracked, but only weak keys and that flaw was addressed and fixed by WPA.
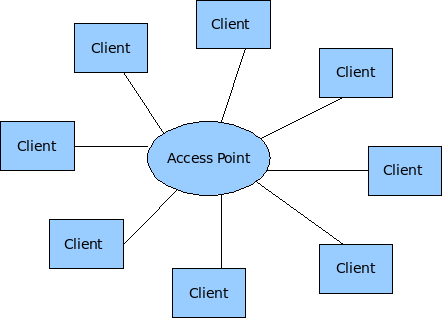
Wireless adapters on Unix Systems can operate in three different modes: Client, Hostap (Access Point) and Adhoc mode. Most of the implementations of wireless (802.11) networks are based on a model where there is one Access Point with several wireless clients attached to to it.
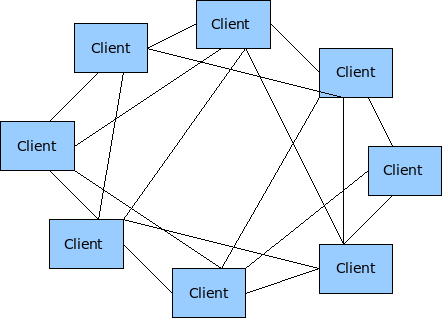
Wireless Mesh networks make use of the less tested Adhoc mode of 802.11.
WEP and WPA requires a couple of kld's to be loaded before they can be configured. The following kld's should be added to loader.conf
wlan_acl_load="YES"
wlan_amrr_load="YES"
wlan_ccmp_load="YES"
wlan_tkip_load="YES"
wlan_wep_load="YES"
wlan_xauth_load="YES"
WEP
Enable and test WEP in Adhoc mode on the HPN. WEP makes use of a single PSK that needs to be configured on all the wireless nodes. Any node or wireless device that is configured with this PSK will have the capability to crypt and decrypt these wireless packets. There are two methods to configure WEP in FreeBSD. You can use either use ifconfig directly or you can make use of the WPA supplicant utility.
ifconfig e.g.
mesh-9e69:~ # ifconfig ath0 10.10.1.2/24 wep deftxkey 1 wepkey 128bitwepison
mesh-9e69:~ # ifconfig ath0
ath0: flags=8843<UP,BROADCAST,RUNNING,SIMPLEX,MULTICAST> metric 0 mtu 1500
ether 00:80:48:50:9e:69
inet6 fe80::280:48ff:fe50:9e69%ath0 prefixlen 64 scopeid 0x1
inet6 fd9c:6829:597c:20:280:48ff:fe50:9e69 prefixlen 64
inet6 fd9c:6829:597c:20:: prefixlen 64 anycast
inet 10.10.1.2 netmask 0xffffff00 broadcast 10.10.1.255
media: IEEE 802.11 Wireless Ethernet autoselect mode 11g <adhoc>
status: associated
ssid ptamesh channel 13 (2472 Mhz 11g) bssid 56:e5:be:30:14:5a
authmode OPEN privacy ON deftxkey 1 wepkey 1:104-bit txpower 31.5
scanvalid 60 bgscan bgscanintvl 300 bgscanidle 250 roam:rssi11g 7
roam:rate11g 5 protmode CTS burst
Test configuration:
Host A ----- wep ------- Host B ----- wep Host C
Enable WEP on three mesh nodes and test connectivity.
mesh-9e69:~ # ping6 ff02::1%ath0 16 bytes from fe80::280:48ff:fe50:9e69%ath0, icmp_seq=87 hlim=64 time=2.122 ms 16 bytes from fe80::280:48ff:fe50:9ddd%ath0, icmp_seq=87 hlim=64 time=5.625 ms(DUP!) 16 bytes from fe80::280:48ff:fe50:9a44%ath0, icmp_seq=87 hlim=64 time=32.358 ms(DUP!)
Everything seems to work fine (as expeted) with WEP enabled in the mesh.
WPA
WPA was designed to work in an environment where you have one AP and several clients and not for Adhoc (mesh) networks. On the AP you have the Authenticator software and on the client you have the supplicant software. This means that if one would like to use WPA to it's full then every mesh node needs to be an Authenticator for all the other nodes it can see, as well as a supplicant for every node it can see. According to the WPA design document http://wirelessafrica.meraka.org.za/wiki/images/3/39/Wpa_supplicant-devel-04.pdf one can use WPA in Adhoc mode only in a static way with PSK's:
IEEE 802.11 operation mode (Infrastucture/IBSS). 0 = infrastructure (Managed) mode, i.e., associate with an AP. 1 = IBSS (ad-hoc, peer-to-peer) Note: IBSS can only be used with key_mgmt NONE (plaintext and static WEP) and key_mgmt=WPA- NONE (fixed group key TKIP/CCMP). In addition, ap_scan has to be set to 2 for IBSS. WPA-None requires following network block options: proto=WPA, key_mgmt=WPA-NONE, pairwise=NONE, group=TKIP (or CCMP, but not both), and psk must also be set (either directly or using ASCII passphrase).
This is methods is very similar to the way that WEP is being used. This means the the only advantage of using WPA over WEP is that one can make use of the AES encryption engine that comes with WPA. Please note that with this mode of WPA and with WEP that anyone can decrypt the data being send over the air if they get hold of the mesh-wide PSK that is configured on every node in the network. If security is of importance them end users should consider the use of point-to-point security mechanisms like VPN's.
The configuration of WPA is not supported in command line mode, but only with the wpa_supplicant software. This is an example of a wpa_supplicant.conf file to enable WPA in Adhoc mode:
ap_scan=2
#
network={
ssid="ptamesh"
# Channel 13 : 2472 Mhz 11g
frequency=2472
mode=1
proto=WPA
key_mgmt=WPA-NONE
pairwise=NONE
group=TKIP
psk="mesh-ipv6"
}
To start the WPA software during boot-up one needs to add WPA to the ifconfig line in rc.conf. E.g.
ifconfig_ath0="WPA 10.10.1.1/24 mode 11g mediaopt adhoc channel 13 ssid ptamesh"
Test configuration:
Host A ----- wep ------- Host B ----- wep Host C
Unfortunately WPA did not work as easy as WEP, so it's off to debugging.
Starting wpa_supplicant in the foreground with debugging enabled. E.g
wpa_supplicant -d -i ath0 -c /etc/wpa_supplicant.conf
The debugging output shows that something happens that initiates a wlan scan operation, while the card is in Adhoc mode. This should not happen and wpa_supplicant software never completes the configuration due to this error.
mesh-9ddd:~ # wpa_supplicant -d -i ath0 -c /etc/wpa_supplicant.conf Initializing interface 'ath0' conf '/etc/wpa_supplicant.conf' driver 'default' ctrl_interface 'N/A' bridge 'N/A' Configuration file '/etc/wpa_supplicant.conf' -> '/etc/wpa_supplicant.conf' Reading configuration file '/etc/wpa_supplicant.conf' ap_scan=2 Priority group 0 id=0 ssid='ptamesh' Initializing interface (2) 'ath0' EAPOL: SUPP_PAE entering state DISCONNECTED EAPOL: KEY_RX entering state NO_KEY_RECEIVE EAPOL: SUPP_BE entering state INITIALIZE EAP: EAP entering state DISABLED EAPOL: External notification - portEnabled=0 EAPOL: External notification - portValid=0 Own MAC address: 00:80:48:50:9d:dd wpa_driver_bsd_set_wpa: enabled=1 wpa_driver_bsd_set_wpa_internal: wpa=3 privacy=1 wpa_driver_bsd_del_key: keyidx=0 wpa_driver_bsd_del_key: keyidx=1 wpa_driver_bsd_del_key: keyidx=2 wpa_driver_bsd_del_key: keyidx=3 wpa_driver_bsd_set_countermeasures: enabled=0 wpa_driver_bsd_set_drop_unencrypted: enabled=1 Setting scan request: 0 sec 100000 usec Added interface ath0 State: DISCONNECTED -> SCANNING Trying to associate with SSID 'ptamesh' Cancelling scan request WPA: clearing own WPA/RSN IE Automatic auth_alg selection: 0x1 wpa_driver_bsd_set_auth_alg alg 0x1 authmode 1 WPA: No WPA/RSN IE available from association info WPA: Set cipher suites based on configuration WPA: Selected cipher suites: group 8 pairwise 1 key_mgmt 16 proto 1 WPA: clearing AP WPA IE WPA: clearing AP RSN IE WPA: using GTK TKIP WPA: using PTK NONE WPA: using KEY_MGMT WPA-NONE WPA: Set own WPA IE default - hexdump(len=24): dd 16 00 50 f2 01 01 00 00 50 f2 02 01 00 00 50 f2 00 01 00 00 50 f2 00 No keys have been configured - skip key clearing wpa_driver_bsd_set_key: alg=TKIP addr=ff:ff:ff:ff:ff:ff key_idx=0 set_tx=1 seq_len=6 key_len=32 wpa_driver_bsd_set_drop_unencrypted: enabled=1 State: SCANNING -> ASSOCIATING wpa_driver_bsd_associate: ssid 'ptamesh' wpa ie len 24 pairwise 0 group 2 key mgmt 4 ioctl[SIOCS80211, op 22, len 24]: Invalid argument Association request to the driver failed wpa_driver_bsd_set_key: alg=TKIP addr=ff:ff:ff:ff:ff:ff key_idx=0 set_tx=1 seq_len=6 key_len=32 Cancelling authentication timeout State: ASSOCIATING -> COMPLETED CTRL-EVENT-CONNECTED - Connection to 00:00:00:00:00:00 completed (auth) [id=-1 id_str=] EAPOL: External notification - portControl=ForceAuthorized
Next was to install fresh copy of the FreeBSD src code onto my PC. I found the wpa_supplicant source code under /usr/src/usr.sbin/wpa/wpa_supplicant/driver_freebsd.c Build a new driver from source code and run it on a router. After that I've added in a lot of printf statements to trace how the driver works and to locate the code that puts the wifi card in scanning mode. In the end I found out that wpa_supplicant driver did not put the card in scanning mode, but it somehow caused the 802.11 stack to start the scanning. Unfortunately I don't know enough about the 802.11 code in FreeBSD to do any mode debugging. I've send a mail about the problem to one of the FreeBSD mailing lists and the originator of most of the 802.11 code in FreeBSD (Sam Leffler) said I must log a problem report. So I logged a problem report with FreeBSD and now we have to wait and see if someone to take responsibility to fix this problem. More information on the problem report can be found at: http://www.freebsd.org/cgi/query-pr.cgi?pr=126822
For now I recommend that we make use of WEP instead of WPA in our implementation as it is working and there isn't such a big advantage in using WPA over WEP in this mode except for the encryption algorithm that changes from WEP to AES.
Voip - IP04
High performance node page
Installing cacti on FreeBSD
Recipe to install FreeBSD, add ports mysql, php5 and cacti: http://wirelessafrica.meraka.org.za/wiki/index.php/Image:Installing_Cacti_on_FreeBSD.zip
If you intall it for the first time, you may have to follow this steps to make it work correctly:
1. Create the MySQL database:
# mysqladmin --user=root create cacti
2. Create a mysql user/password for cacti:
(change user and/or password if requered)
# echo "GRANT ALL ON cacti.* TO cactiuser@localhost IDENTIFIED BY 'cactiuser'; F LUSH PRIVILEGES;" | mysql
3. Import the default cacti database:
# mysql cacti < /usr/local/share/cacti/cacti.sql
4. Edit /usr/local/share/cacti/include/config.php.
5. Add a line to your /etc/crontab file similar to:
*/5 * * * * cacti /usr/local/bin/php /usr/local/share/cacti/poller.php > /dev/nu ll 2>&1
6. Add alias in apache config for the cacti dir:
Alias /cacti "/usr/local/share/cacti/"
7. Be sure apache gives an access to the directory ('Allow from' keywords).
8. Open a cacti login page in your web browser and login with admin/admin.
Add the following line in the end of httpd.conf vi /usr/local/etc/apache22/httpd.conf Include etc/apache/Includes/*.conf
vi /usr/local/etc/cacti.conf Alias /cacti/ "/usr/local/share/cacti/" <Location /cacti> AddHandler php-script php DirectoryIndex index.php AllowOverride None Order allow,deny Allow from all </Location>
Community wireless networks page
Putting FreeBSD onto my EeePC
OK, finally get around to it. First read John's info on the wiki: http://wiki.meraka.csir.co.za/wiki/index.php/Category:ASUS_eeePC
Then copy John's FreeBSD EeePC distribution (img.tgz) to my PC. Follow Werner's instructions to get the distro on USB memory stick
fdisk -I da0 fdisk -B da0 bsdlabel -w da0s1 auto bsdlabel -B da0s1 newfs /dev/da0s1a mount /dev/da0s1a /mnt tar -xvf img.tgz -C /mnt/ echo /dev/da0s1a / ufs rw 1 1 > /mnt/etc/fstab echo ifconfig_DEFAULT=DHCP > /mnt/etc/rc.conf echo hostname=demo >> /mnt/etc/rc.conf umount /mnt
Plug into USB port on EeePC. Select boot form USB (Press ESC at bootup to get menu) Boot FreeBSD Dump WinXP image on a USB disk
dd if=/dev/ad2 of=/dev/da2 bs=4k
Follow instructions above to get FreeBSD on ad2
fdisk -I ad2 fdisk -B ad2 bsdlabel -w ad2s1 auto bsdlabel -B ad2s1 newfs -U /dev/ad2s1a mount /dev/ad2s1a /mnt tar -cf - --exclude /mnt / | tar -xvpf - -C /mnt echo /dev/ad2s1a / ufs rw 1 1 > /mnt/etc/fstab
Enable ipv6, ssh and moused in /etc/rc.conf
ipv6_enable="YES" sshd_enable="YES" moused_enable="YES"
Shutdown and reboot.
Install Xorg and KDE
setenv PACKAGEROOT ftp://ftp2.za.freebsd.org pkg_add -r xorg pkg_add -r kde-lite
Enable and test sound. Add the following line in /boot/loader.conf
snd_hda_load="YES"
Search for app that can show the battery status in X. Install and test desktopbsd-tools. Battery status works. Test wifi install gui. Not impressed, it only supports WEP
pkg_add -r desktopbsd-tools
Battery status works. Test wifi install gui. Not impressed, it only supports WEP. Delete package and search for other battery apps. See that KDE has a package that can show battery status. Install klaptopdaemon.
pkg_add -r kdeutils-klaptopdaemon
Battle to get it to work. Eventually find out that you have to load AMP (advanced power management). Edit /etc/rc.conf and add the following lines.
amp_enable="YES" ampd_enable="YES"
Shutdown and reboot
Login and start KDE. Enable battery monitor under kde "Start" "Settings" "Power control" "Laptop Battery". Yes, I get a new battery icon. Remove power and test it. Battery shows power, but reporting of "time left" is broken.
Enable power manager to preserve power while running on battery. Add following to rc.conf
powerd_enable="YES"
and lower CPU speed. Add the following to /etc/sysctl.conf
dev.cpu.0.cx_lowest=C3
Try to get dstumbler to work so that we can use the EeePC as a wireless measurement PC. Install BSD-airtools (dstumbler part of it), but it looks like the package is broken. Search for other packages that we can use, but I can't find anything. Start looking at what command line stats available.
Try to enable virtual screen resolution in Xorg. Add the following in the Screen section of xorg.conf
SubSection "Display"
Viewport 0 0
Depth 24
Virtual 1200 720
EndSubSection
Restart X, but it doesn't work. Do a lot of reading and playing, but I cannot get it to work.
Meraka wireless Network
We are making use of Linksys WRT54 wifi routers, re-flashed with dd-wrt software. We've also enabled WPA corporate mode, using a Radius server that verify users against the CSIR LDAP server.
Upgrading the dd-wrt firmware on a linksys.
Firmware upgrades are usually done via the WEB gui. Here is the instructions to do it on the command line. It's important to know how to do it, so that we can script it in future. Fist enable ssh via the WEB gui. You can find it under Administrator -> Services -> Secure Shell. Select SSHd en then add your ssh public key under the Authorized Keys section. Save settings. Now you can login without a password as well run remotes commands via ssh.
scp ftp/linksys/dd-wrt/dd-wrt.v24_std_generic.bin root@192.168.1.1:/tmp ssh root@192.168.1.1 "write /tmp/dd-wrt.v24_std_generic.bin linux" ssh root@192.168.1.1 reboot
Load WEB gui and verify if upgrade worked. Yes - all new.